The US Govt 5 years ago: e2e encryption is for terrorists. The govt should have backdoors.
The US Govt now: Oh fuck, our back door got breached, everyone quick use e2e encryption asap!
The Australian government tried to straight up ban encryption some years ago.
Different parts of the government. Both existed then and now. There has for a long time been a substantial portion of the government, especially defense and intelligence, that rely on encrypted comms and storage.
It’s probably also good practice to assume that not all encrypted apps are created equal, too. Google’s RCS messaging, for example, says “end-to-end encrypted”, which sounds like it would be a direct and equal competitor to something like Signal. But Google regularly makes money off of your personal data. It does not behoove a company like Google to protect your data.
Start assuming every corporation is evil. At worst you lose some time getting educated on options.
End to end is end to end. Its either “the devices sign the messages with keys that never leave the the device so no 3rd party can ever compromise them” or it’s not.
Signal is a more trustworthy org, but google isn’t going to fuck around with this service to make money. They make their money off you by keeping you in the google ecosystem and data harvesting elsewhere.
google isn’t going to fuck around with this service to make money
Your honor, I would like to submit Exhibit A, Google Chrome “Enhanced Privacy”.
Google will absolutely fuck with anything that makes them money.
This. Distrust in corporations is healthy regardless of what they claim.
Thats a different tech. End to end is cut and dry how it works. If you do anything to data mine it, it’s not end to end anymore.
Only the users involved in end to end can access the data in that chat. Everyone else sees encrypted data, i.e noise. If there are any backdoors or any methods to pull data out, you can’t bill it as end to end.
You are suggesting that “end-to-end” is some kind of legally codified phrase. It just isn’t. If Google were to steal data from a system claiming to be end-to-end encrypted, no one would be surprised.
I think your point is: if that were the case, the messages wouldn’t have been end-to-end encrypted, by definition. Which is fine. I’m saying we shouldn’t trust a giant corporation making money off of selling personal data that it actually is end-to-end encrypted.
By the same token, don’t trust Microsoft when they say Windows is secure.
Its a specific, technical phrase that means one thing only, and yes, googles RCS meets that standard:
https://support.google.com/messages/answer/10262381?hl=en
How end-to-end encryption works
When you use the Google Messages app to send end-to-end encrypted messages, all chats, including their text and any files or media, are encrypted as the data travels between devices. Encryption converts data into scrambled text. The unreadable text can only be decoded with a secret key.
The secret key is a number that’s:
Created on your device and the device you message. It exists only on these two devices.
Not shared with Google, anyone else, or other devices.
Generated again for each message.
Deleted from the sender’s device when the encrypted message is created, and deleted from the receiver’s device when the message is decrypted.
Neither Google or other third parties can read end-to-end encrypted messages because they don’t have the key.
They have more technical information here if you want to deep dive about the literal implementation.
You shouldn’t trust any corporation, but needless FUD detracts from their actual issues.
You are missing my point.
I don’t deny the definition of E2EE. What I question is whether or not RCS does in fact meet the standard.
You provided a link from Google itself as verification. That is… not useful.
Has there been an independent audit on RCS? Why or why not?
Not that I can find. Can you post Signals most recent independent audit?
Many of these orgs don’t post public audits like this. Its not common, even for the open source players like Signal.
What we do have is a megacorp stating its technical implementation extremely explicitly for a well defined security protocol, for a service meant to directly compete with iMessage. If they are violating that, it opens them up to huge legal liability and reputational harm. Neither of these is worth data mining this specific service.
They can just claim archived or deleted messages don’t qualify for end to end encryption in their privacy policy or something equally vague. If they invent their own program they can invent the loophole on how the data is processed
Or the content is encrypted, but the metadata isn’t, so they can market to you based on who you talk to and what they buy, etc.
This part is likely, but not what we are talking about. Who you know and how you interact with them is separate from the fact that the content of the messages is not decryptable by anyone but the participants, by design. There is no “quasi” end to end. Its an either/or situation.
Provided they have an open API and don’t ban alternative clients, one can make something kinda similar to TOR in this system, taking from the service provider the identities and channels between them.
Meaning messages routed through a few hops over different users.
Sadly for all these services to have open APIs, there needs to be force applied. And you can’t force someone far stronger than you and with the state on their side.
The messages are signed by cryptographic keys on the users phones that never leave the device. They are not decryptable in any way by google or anyone else. Thats the very nature of E2EE.
How end-to-end encryption works
When you use the Google Messages app to send end-to-end encrypted messages, all chats, including their text and any files or media, are encrypted as the data travels between devices. Encryption converts data into scrambled text. The unreadable text can only be decoded with a secret key.
The secret key is a number that’s:
Created on your device and the device you message. It exists only on these two devices.
Not shared with Google, anyone else, or other devices.
Generated again for each message.
Deleted from the sender’s device when the encrypted message is created, and deleted from the receiver’s device when the message is decrypted.
Neither Google or other third parties can read end-to-end encrypted messages because they don’t have the key.
They cant fuck with it, at all, by design. That’s the whole point. Even if they created “archived” messages to datamine, all they would have is the noise.
Exactly. We know corporations regularly use marketing and doublespeak to avoid the fact that they operate for their interests and their interests alone. Again, the interests of corporations are not altruistic, regardless of the imahe they may want to support.
Why should we trust them to “innovate” without independent audit?
Signal doesn’t harvest, use, sell meta data, Google may do that.
E2E encryption doesn’t protect from that.
Signal is orders of magnitude more trustworthy than Google in that regard.There’s also Session, a fork of Signal which claims that their decentralised protocol makes it impossible/very difficult for them to harvest metadata, even if they wanted to.Tho I personally can’t vouch for how accurate their claims are.
Agreed. That still doesnt mean google is not doing E2EE for its RCS service.
Im not arguing Google is trustworthy or better than Signal. I’m arguing that E2EE has a specific meaning that most people in this thread do not appear to understand.
Sure!
I was merely trying to raise awareness for the need to bring privacy protection to a level beyond E2EE, although E2EE is a very important and useful step.
End to end matters, who has the key; you or the provider. And Google could still read your messages before they are encrypted.
You have the key, not the provider. They are explicit about this in the implementation.
They can only read the messages before encryption if they are backdooring all android phones in an act of global sabotage. Pretty high consequences for soke low stakes data.
I mean, Google does, with Play Services.
You may be right for that particular instance, but I’d still argue caution is safer.
Of course our app is end-to-end encrypted! The ends being your device and our server, that is.
It’s end to end to end encrypted!
If its not Open Source and Audited yearly, its compromised. Your best option for secure comms is Signal and Matrix.
End-to-end encryption matters if your device isn’t actively trying to sabotage your privacy.
If you run Android, Google is guilty of that.
If you run Windows in a non-enterprise environment Microsoft is guilty of that.
If you run iOS or MacOS, Apple is (very likely) guilty of that.
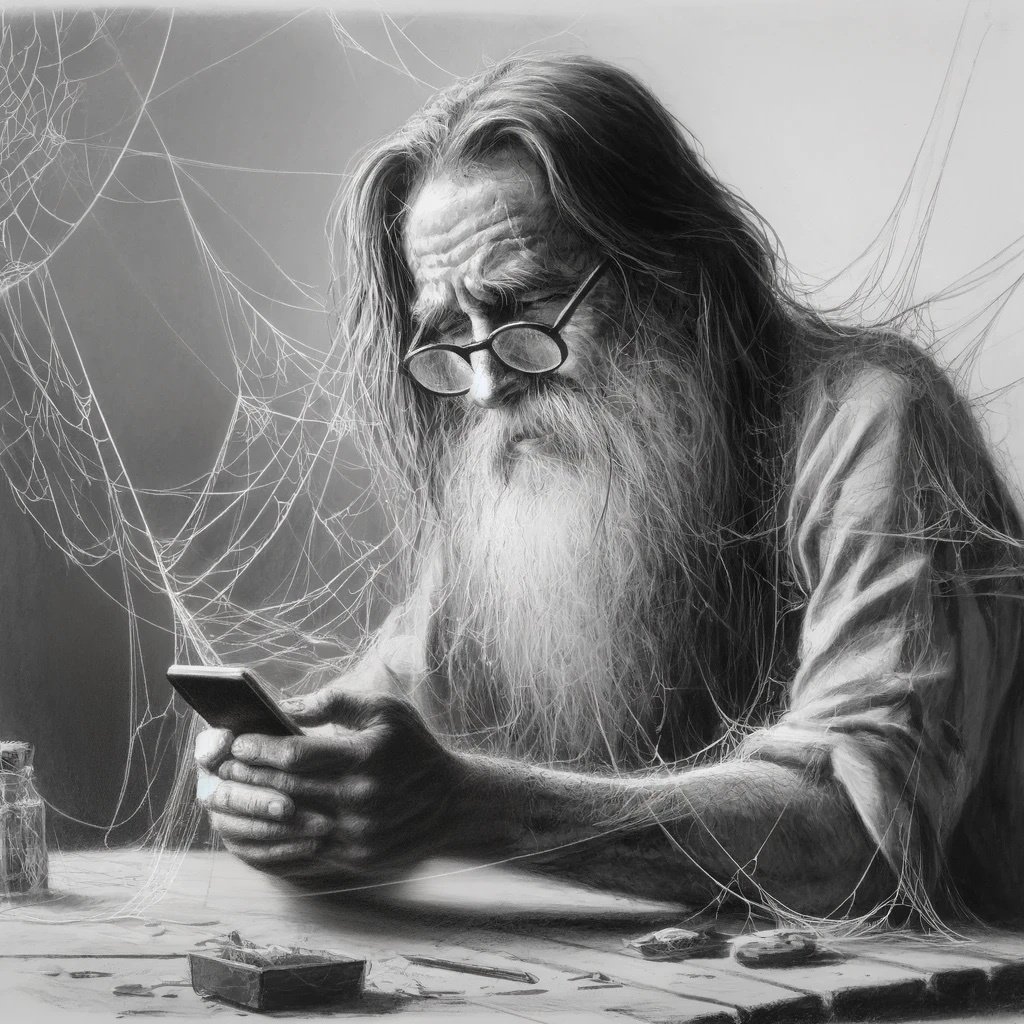
Everybodies aunt at thanksgiving:
“I should be fine. I only trust the facebook with my information. Oh, did I tell you? We have 33 more cousins we didn’t know about. I found out on 23andme.com. All of them want to borrow money.”
Real encrypted apps, …or just the ones their own government can use to spy on them?
In the voice of Nelson Muntz: “Nobody spies on our citizens but us!”
The reporter mentioned signal, though the gov spokespeople didn’t seem to recommend any specific app
End-to-end encryption is indispensable. Our legislators (no matter where we live) need to be made to understand this next time they try to outlaw it.
“So it’s like a filter on the tubes?” - Our legislators
“you wouldn’t put a dump truck full of movies on a snowy road without chains on the tires would you?”
On January 20th: The cyberattack is coming from inside the house!
Dumbfuck and his cronies now have access to PRISM and ECHELON. Again.
I use a one time pad with all of my contacts. I ask them to eat or burn each page when they are used up.
The same people who want to get rid of encryption
I mean, clearly not the SAME people.
What i read [and corrected] from the article :
“The hacking
campaign[group], nicknamed [ by Microsoft ] Salt Typhoonby Microsoft,
[ this actual campaign of attacks ] is one of the largest intelligence compromises in U.S. history, and not yet fully remediated. Officials in a press call Tuesday [ 2024-12-3 ] refused to set a timetable for declaring the country’s telecommunications systems free of interlopers. Officials had previously told NBC News that China hacked AT&T, Verizon and Lumen Technologies to spy on customers.”Hear me out, maybe we should update pots and sms to have optional end-to-end encryption for modern implementations as well…Optional as backwards compatible and clearly shown as unencrypted when used that way to be clear.
Att won’t make money off that unless they offer it as a paid service. No reason to give that away for free and the other cell carriers can just pay off (bribe with campaign contributions) legislators to understand encryption is “too costly to implement at such a scale”
There’s been a lot of good research done lately on how to achieve trusted communication on untrusted platforms and over untrusted channels. Encryption is a big part of that.
And there are a number of scenarios where the ISP creates a hostile environment without having been compromised by an external actor. A malicious government, for example, or an ISP wanting to exploit customer communications for commercial reasons.
Hey you guys remember that big AT&T breach recently?
deleted by creator
Question for more tech savvy people: should I be worried about wiping old data, and if so for which apps? Just messaging apps, or also email and social media? Or can I just use the encrypted apps moving forward?
the safest perspective to have is this -
every single thing you send online is going to be there forever. “the cloud” is someone’s server and constitutes online. even end to end encryption isn’t necessarily going to save you.
for example iCloud backup is encrypted. but Apple in the past has kept a copy of your encryption key on your iCloud. why? because consumers who choose to encrypt and lose their passwords are gonna freak out when all their data is effectively gone forever.
so when FBI comes a’knocking to Apple with a subpoena… once they get access to that encryption key it doesn’t matter if you have the strongest encryption in the world
my advice
never ever ever write something online that you do not want everybody in the world seeing.
to put on my tin foil hat, i believe government probably has access to methods that break modern encryptions. in theory with quantum computers it shouldn’t be difficult
I agree with you and I don’t put anything that I would consider questionable online, at least not these days. I’m just having a hard time figuring out what adjustments to make in addition to worrying about personal things I’ve already shared, like my gender and race. You know what I mean? I’m a married woman, and I have info in various places about our family planning choices, to give an example. That’s really starting to worry me, but how can I even begin to delete my data? It’s everywhere. Every doctor has their own patient portal, I have multiple email accounts, and I don’t even want to think about the dumb shit I might have posted when YouTube comment sections were new.
It’s all really overwhelming.
yeah i just try not to think about it. I’m glad I was in the myspace generation during my teenage years. so I was actually able to just delete my myspace later on as an adult
i feel worse for the kids growing up today. they don’t fully understand the implications of what they are posting online. anything and everything is being recorded forever. my generation got a chance to be a stupid kid and have it be forgotten. today’s kids don’t get that opportunity
the best you can do, though, is just stop posting potentially damaging things online. you can’t change what you already posted. and 999 times out of a thousand, it’s not gonna hurt you.
i understand the overwhelmed feeling though
Thanks, I appreciate the commiserating, it does make me feel a little better.
Just stop using your electronic devices. Not like they don’t all have monitors built in already anyway. Every connected device could be sending screenshots home and we’d never know. I mean, I guess you could use something like Wireshark to monitor your home network, but something tells me nowadays there are ways around even that. I’m not a certified network tech or even a script kiddie, but I don’t trust my tech as far as my dog can throw it. I just try to secure through obfuscation as much as possible. Everyone thinks I have carbon monoxide poisoning, but it’s a small price to pay for peace of mind - even a small one.
deleted by creator
I’m just saying that, unless you built the device you’re using, and you know what every component does, and you know what it’s doing when, and you know it wasn’t manufactured by a foreign state-owned manufacturer with a penchant for putting spy chips in their devices, then you can’t truly trust anything you do on it, encrypted or not. It doesn’t really matter, if the software is being encrypted by backdoored hardware.
deleted by creator
Oh yeah for sure. Gang gang.
Do what the Germans did in ww1 when they knew their diplomatic code was broken but couldn’t change it. They put the important stuff in plain sight and treated it like junk mail and encoded the boring stuff.
That’s what I’m sayin. Or if nothing else just fill the airwaves with garbage.